More than four million personal records of US government workers are thought to have been hacked and stolen, it has been. With US investigators blaming the Chinese government (although the Chinese deny involvement), this incident shows how data could be the new frontier for those in cyberspace with a political agenda.
In April 2015, the US Office of Personnel Management (OPM) – the body that provides the human resources function for the federal government and is responsible for background checks for security clearances – realised its records had been hacked.
Along with the direct personnel details, there are a whole range of references and contacts contained in the OPM records. The sensitive data could be used to identify people with security clearances, and could be used for the impersonation or blackmail of federal employees. Someone with security clearance could be exposed to identity fraud, where an intruder could gain access to sensitive information using the stolen identifies.
The data could also be used to hack into other government sites. For example, intruders recently attempted to breach the Inland Revenue Service’s systems (this time it was blamed on Russia) using personal information taken from tax returns stolen during other commercial breaches.
Such attacks create a certain amount of national humiliation. The hacking of confidential data from Sony highlighted how embarrassing it can be for information to leak. The contents of its sensitive emails are now searchable on Wikileaks, and we have probably only seen the tip of the iceberg in terms of the data that was taken.
How did the hackers beat the system?
Aware of the threat of attack, the OPM said it has “undertaken an aggressive effort” to improve its cybersecurity over the last year. So why, many might ask, did it take the government so long to detect the security breach?
Many large companies now use advanced intrusion detection systems (IDS) that raise alerts of possible security breaches that are then collected, logged and analysed. At the OPM, the system that detected the breach was called EINSTEIN. It was developed by a division of the Department of Homeland Security to monitor the exit points of US government by examining the packets carried around a network for possible signs of intrusion.
The growing threat of attacks has led to the use of tools that gather all the event logs from IDS agents on a network. Human analysts then have to make sense of the events coming in, in order to spot possible signs of an intrusion. To do this advanced computer systems filter down the event logs and present only the most important ones to the analysts.
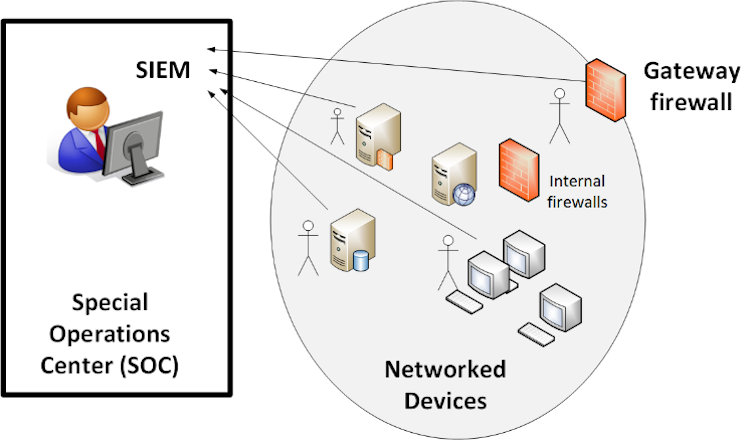
Unfortunately some of the tell-tale signs of an intrusion could be lost. In the case of EINSTEIN, the system has to monitor the gateways devices coming from each of the partner government agencies, where it might be difficult to detect an intruder who has remote access to the inside of one the networks.
It is common for an IDS to detect where there are high rates of data loss (which large amounts of data are filtered off the network). So if this data loss is fairly slow, the IDS will often not detect it. The system must be tuned to show standard signs of intrusions so it does not trigger too many alerts and swamp its human administrators. Cyber attackers, however, often understand these standard detection methods and will use ways to slowing down the intrusion and avoid being noticed.
Many networks use a firewall to separate servers that can be accessed from untrusted networks from the protected main network infrastructure is then protected on another network. In many large networks, IDS agents exist across the whole network and listen for possible intrusions. The problem is that an intruder can often get over the firewall, and then remotely access the protected systems. Many organisations also allow employees to access their computer remotely through a secure network connection. With stolen access details, an intruder can use this remote access path in the same way.
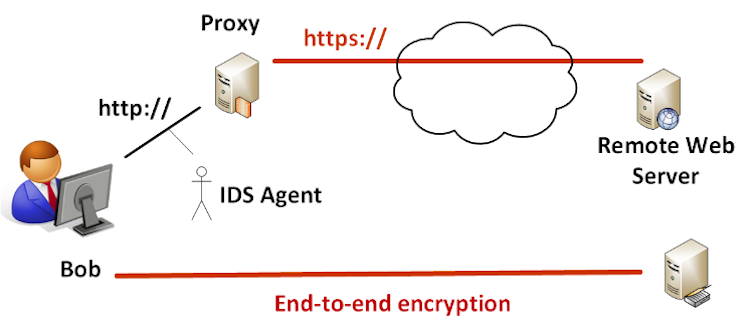
The other major weakness of many IDSs is that they cannot examine the contents of encrypted data packets, such as where users visit secured websites starting with “https://”. To overcome this, many systems ban direct secure connections and route the data via a proxy, where they can examine the packets between the user’s computer and the secure connection to the internet. Unfortunately, intruders can set up connections using what is known as an end-to-end encryption tunnel that bypass this provision and in which data loss cannot be detected by the proxy or IDS.
While it has not been proven that the most recent attack was driven by a political agenda, the information once leaked from a site can then be sold on for the purposes of compromising nation states. Governments still need to understand the risks around their documents and make sure there are effective safeguards in place to restrict access to sensitive information. They often have a lot to learn from high-risk companies, such as in the finance sector, where there is often large-scale detection of intrusions and monitoring for data loss.
The US agencies are saying that all those affected by the hack of the OPM will be insured against any loss they might experience as a result. But data is the life blood of most organisations and probably one of its important assets, so the need for improved security increases by the day.

