There is some controversy about what we mean by the word “hacker”. Historically, and as far back as the 1960s, a hacker was someone who was an expert programmer. But today, it is a word generally used to describe someone involved in illegal activity using computers.
The two are of course linked. Hackers in either sense of the word are experts and very skilled individuals. But there is obviously an important difference.
While the word hacker has evolved from meaning something potentially innocent to something almost definitely illegal, many people who might be seen as hackers have moved in the opposite direction. Some of the biggest names in the technology industry today once got their hands dirty with their skills.
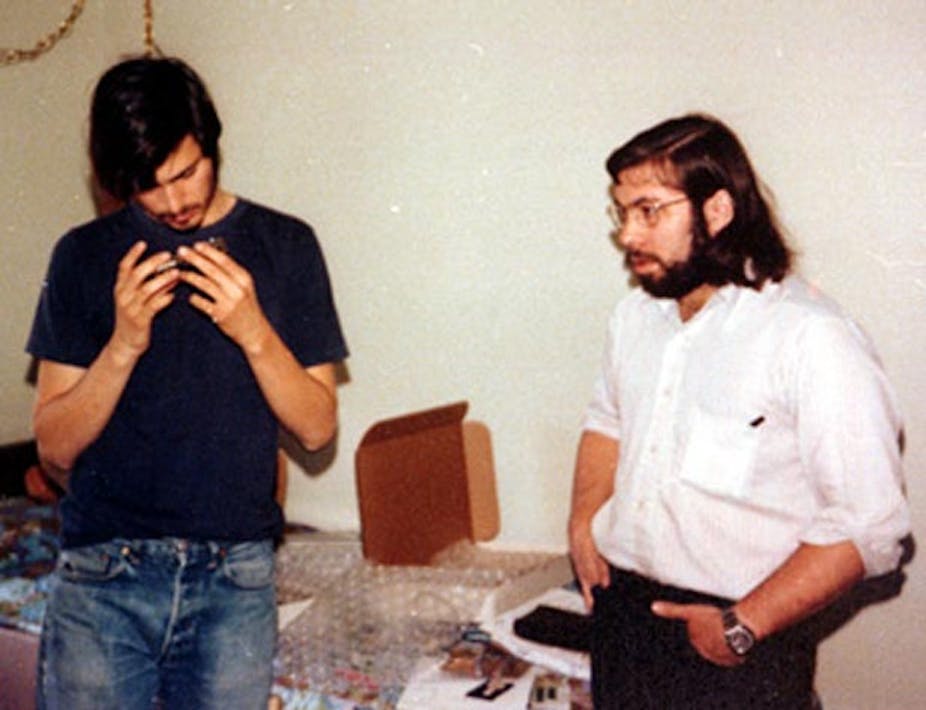
On display at the Computer History Museum in Mountain View, California is a device called a Blue Box. It was a device used to interrupt phone signals and was invented by two very skilled hackers – Steve Wozniak and Steve Jobs. You may have heard of them.
What’s a Blue Box?
The Blue Box that the two Steves built belongs to a type of hacking activity called phone phreaking.
A telephone system comprises a number of interconnected telephone exchanges. When you dial the number of someone you want to speak to, each exchange along the route has to establish a connection to put your call through. In the early days of the telephone, this was done by human operators but as technology evolved, automatic exchanges were introduced and the human operator disappeared.

These automatic exchanges still need to communicate with each other in order to route your call to its destination. This process is known as signalling and was done using a series of audible tones when it was first introduced in the US during the 1960s and 1970s.
These tones proved to be an Achilles heel just waiting to be exploited by the hackers of the day.
The blue box was designed to emulate the in-band signalling tones used by the telephone exchanges. Playing these tones through a speaker connected to the telephone handset’s microphone fooled the automatic exchanges into thinking that they were receiving legitimate signalling information. And once all of the signalling codes were known and understood by the hacker, anything was possible.
They could determine the route taken by a call, you can override the charging and hence, billing processes and overcome any blocking restrictions that are in place. This then is what Steve Wozniak and Steve Jobs designed in the early 1970s and began to sell clandestinely. Going by the names of Berkeley Blue and Oaf Tobar, the Steves entered the illegal world of the Phone Phreaker.
When the rich and famous break the law, we often wonder what their motivations were. Watching the various videos and reading interviews that exist of the two of them describing this period in their lives, it is clear that they were at first excited by the technical challenge but of course, they soon also realised that money could be made from their work.
They eventually abandoned their criminal ways after having almost been caught and no doubt by then were already motivated by new technical challenges. Steve Jobs would later claim that there would have been no Apple, had he and Wozniak not experimented with Blue Boxes.
This branch of hacking was ultimately brought to an end when the telephone companies adopted out-of-band signalling where separate and dedicated connections were used for exchange to exchange communication.
So, which definition do we apply to Wozniak and Jobs? Were they skilled programmers? Yes. Were they knowingly engaged in illegal activity with their Blue Box? Yes. Would we class either of them as a hacker now? Almost certainly not. They are household names for very different reasons.
Of course, things could have worked out very differently for Steve and Steve. Imagine they had been up to no good with their blue box today, in the post-NSA-scandal world. We’re far less likely to dismiss their antics as harmless rebellion now that we feel more sensitive about our communications.
On the other hand, we have to wonder what they learned during their blue box years that might have contributed to the Apple technologies we use today. Are there hackers out there today dabbling in the dark arts but innovating as they go? Have we already imprisoned the next Steve Jobs for hacking?