Why would thousands of people flock to Las Vegas, right in the middle of summer, when temperatures easily reach the high thirties, to shut themselves up in one of Sin City’s largest hotels without spending any time in its casinos or pools? This is precisely what devotees will do this week to attend DEF CON, one of the world’s largest and longest running hacking conferences.
DEF CON has been running since 1993. It started off as a party for a group of hacker friends and rapidly became the places to be seen for hackers, computer security researchers and security professionals. From its roots as an informal meet up, it has evolved into a summit for thousands of enthusiasts to discuss the latest advances in the field and exchange clever “hacks” - attacks capable of breaking the security of a system.
Where the hackers went, the journalists covering the underground scene soon followed and now federal government employees, or “feds” as they are known, are also in on the game. It didn’t take them long to work out that getting into DEF CON offered a unique opportunity to monitor hackers who break into classified networks but more recently they have realised they can use the event to pick up on the latest tips and recruit people with brilliant technical skills to bat for their team.
The times have changed, and with the years the conference has become more mainstream: it offers several tracks of technical talks, a number of hacking-related (or just fun) contests, and social gatherings. But other elements remain the same. The registration fee continues to be payable by cash only, so that attendees cannot be traced by using electronic payment. The “spot the fed” contest is still popular: attendees hunt down real or imagined spooks that certainly are spying on each and every move the participants make.
Over the years, there have been some notable controversies: technical talks blocked by court injunctions, journalists expelled after trying to covertly recording attendees. This year the controversy reflects a feeling that has spread beyond the world of computer pros - the feds are back in the spotlight in a big way after the NSA spying scandal.
After a long period of playing nicely together, the relationship between hackers and feds has become so strained by recent events that DEF CON organisers have issued a statement saying that the two groups “need some time apart”. DEF CON founder Jeff Moss said he thought it would be best if the feds stay away this year, although DEF CON has since stressed that government types can still come along in a personal capacity if they like.
Even for non-feds, strolling around the conference corridors can be intimidating at first. The gathering has its own stereotypical crowd: skinny, pale, bespectacled young men wearing black t-shirts baring nerd jokes or computer logos (I know, I have been one of them). There are very few women. You can always see small groups of people huddled against walls with their laptops, typing furiously or staring at their screens, oblivious to the tourists crowding the casino halls.
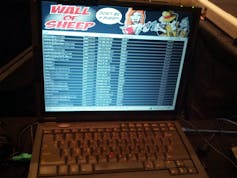
Another classic sight is the “Wall of Sheep”, a projection of the usernames and passwords that have been harvested from unencrypted network connections: people stop by to verify they are not on the wall (and breathe a sigh of relief) or to make fun of friends that should have known better.
When greeting, attendees often go by their nickname; for example, Moss is universally known as The Dark Tangent. They all wear an electronic badge that can be customised at will; at least, by those who are at ease with soldering tools and circuits. The best badge “mod” is displayed in public and awarded a prize in the closing ceremony of the conference.
DEF CON brings chaos to the hotels that host it. Its participants take it upon themselves to install backdoors on as many cashpoint machines as possible, so that they can read debit card information from unsuspecting users, all without raising the suspicion of casino security teams; to crack open the magnetic cards for the hotel rooms; to break into mini bars; and to set up fake access points and gain access to other people’s network traffic. Typically, malice is not the motivation behind these actions: it’s more a desire to show off one’s technical abilities and break the rules.
Official competitions direct the participants’ energy toward sanctioned activities. For example, in the lock picking contest, whoever “breaks” the most locks (think of physical doors or safe locks, here) wins. The capture the flag competition is arguably the world championship in computer hacking: teams of eight to ten people try to outsmart each other by discovering vulnerabilities in custom computer systems and devising exploits to launch against other teams over a three-day non-stop marathon, getting by on little or no sleep with the help of energy drinks and junk food. The coveted black badge, which guarantees life-time free access to the conference, is awarded to the team that wins the competition.
DEF CON is a unique mix of fun and serious hacking. In an industry where so much rides on mutual trust, these meetings can have an important role. Needless to say, any meeting at DEF CON can easily last until the wee hours and is facilitated by prodigal use of alcoholic beverages. The feds may be less welcome this year but they will be back. Both sides know that repairing the damage done by the NSA will be critical for computer security in the future and what better way to bury the hatchet than over a cold beer in a hot desert.

