Mobile phones have become central to our lives. In the US, 90% of adults have one. Although we think of mobile phones for their primary role in communication, they have quietly become a global identification device. Governments, and their secret services and law enforcement agencies in particular, have in most countries moved to prevent individuals from being able to buy a mobile phone without producing official identification. As far as these agencies are concerned, being able to identify the owner of a mobile phone is essential in being able to track the parties in a conversation. For countries like Australia that are considering metadata retention, having people identifiable greaty facilitates the analysis and detection of information of interest.
The problem with requiring identification for purchasing mobile phones is the same problem as for collecting metadata of all citizens in a country, it is not a particularly effective means of stopping or even deterring crime or terrorism but it has a disproportionately large impact on privacy and civil liberties of ordinary people.
Requiring identification to buy pre-paid mobile phones for example has not been shown to increase detection of criminals and has had the opposite effect of creating markets for stolen phones and unidentifiable SIM cards. The sorts of criminals law enforcement and security services would be after would also be generally more than capable of avoiding using phones that they had personally bought. At the same time,
On the flip side, there are a range of scenarios in which law abiding citizens are disadvantaged by the need to produce identification in order to buy a phone. This can range from people who don’t have access to official identification documentation like the homeless, through to people in family situations who don’t have control over their documentation and so are prevented from using it for this purpose.
More insidious however has been the way social networks like Facebook have adopted the mobile phone as a way of preventing anonymity on their networks. Although Facebook does allow just an email to create and verify an account, if a phone number is used, it needs to be a number that has not been used before and is registered with a recognised telecommunications provider. As Facebook states:
“We have limits in place to make sure that everyone is using their real information on their account.”
There is no real way around this. Facebook mobile verification will not work with “virtual phone numbers” such as those that can be set up in different countries to forward to your real phone number or even to a “soft phone”.
In fact, there are services from companies such as Telesign that will do the telephone number verification to ensure that it is a legitimate number from a recognised service provider.
Another consequence of using mobile devices for identification purposes is that it also acts to limit technological advances. The inability to use virtual numbers that might be associated with Skype or other services for the purposes of verification means that ultimately, that flexibility that these services offer is compromised.
Countries like Australia, that have struggled with the population when trying to introduce national identity cards have met with no resistance when introducing proxies for this card and in particular, mandatory identification for mobile phone purchases. The argument for identity cards was given as the need to fight terrorism even though in the last terrorist attack in Australia, the identity and significant information about the terrorist, Monis, was actually known by intelligence services.
Even with this information, the attack went unforeseen. If 18 phone calls to report the individual could not alert the services to an imminent attack, the idea that they will be able to discover this information in metadata is dubious at best.
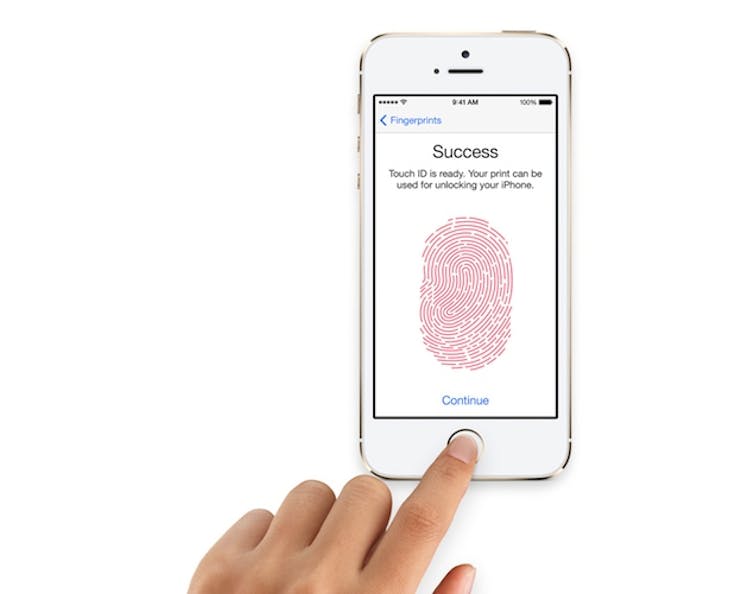
Identification features of the mobile phone have taken a bigger leap with the advent of fingerprint use in the Apple iPhone and other smartphones. The use of the fingerprint links phones to bank details and by design establish the identity of the phone user at any point in time. Of course, Apple, Samsung and other companies will claim that this information is not made available to governments, but post-Snowden, that argument no longer holds very much validity.
The surveillance of a population is an easy option for politicians, even when they struggle to understand the technologies involved. It gives the appearance of using sophisticated means to combat potential threats. It also, like the identification properties of mobile phones, gives a country hidden benefits in control of whistle-blowers and political activists. It also means that these actions can be carried out without oversight, making the abuse of this power almost inevitable.
