Concern over privacy has peaked in recent months, especially in telecommunications, where technological advances appear to bring total surveillance ever closer to reality.
In one high-profile case of recent weeks, Conservative MP David Davis analysed personal metadata obtained from his mobile phone operator and was able to re-build a fairly complete and reasonably detailed record of his movements and behaviour. He argued that if he can do this for himself, the state can do it for everyone else. But there is necessarily a trade off when we demand the best service.
Why are we being watched?
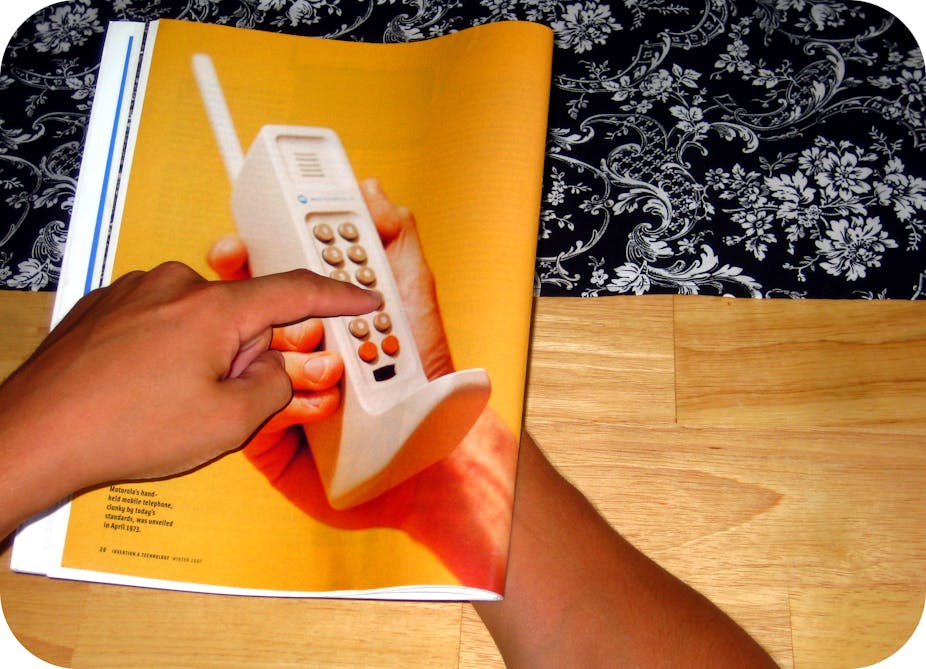
In the days before the mobile phone, life was simple. For those people who owned a telephone, it was connected to a piece of wire, had a phone number that identified its physical location and most importantly, it never moved. The mobile phone changed all this and allowed us to move around as we talked but it also created a significant technical problem that needed to be overcome. If someone calls me using my landline phone at home then my telecommunications provider knows exactly where that phone is and can route the call to it very easily. But what if someone calls me on my mobile? How does the operator know where my mobile phone is, given that it could be anywhere in the world and wherever it is, it will always have the same number? The answer is that mobile operators have to continuously track the location of each mobile phone.
A mobile phone network comprises many thousands of radio base stations, each of which controls mobile phone access within a small geographic area called a cell. In order to route calls to your mobile, an operator must know which cell your mobile is in. It must also know the identity of your mobile to distinguish it from all the others that might be in the same cell and it needs to know who you are to ensure that you are entitled to receive a service from its network. So, whenever your mobile is switched on, your operator knows its identity and location. Take all of this away and you wouldn’t actually be able to have a mobile phone.
The itemisation backlash
Back in 1987, BT announced a major programme to provide itemised billing to its customers. When this started to roll the service out in 1991, there was uproar. At the time, this was less about fears of the state snooping and more about our partners and family finding out too much about our phone habits. Itemised billing is now not only accepted, but has become an important part of customer care because it forms a safeguard against inaccurate charging.
Operators compile itemised bills by recording the phone numbers we dial, the time when those calls were made and their duration. The same is true for text messages. Some text messages may be part of our contract while others might incur a premium charge. To provide an accurate bill, operators have to monitor what we are sending and to whom. Therefore, as part of its normal commercial processes, a mobile phone operator, like any other company, has to keep records of our usage of their service.
Things get a little trickier when it comes to data but the same principles do still apply. The amount of data we download from the internet needs to be monitored for commercial reasons to ensure that we are within the limits of our contracts.
To give us an accurate bill, providers don’t need to know which sites we visit but they could argue that they would like to know what sites we are visiting so that they can plan for future investment and development of their network infrastructure.
So, for example, if they notice that more people are accessing the BBC iPlayer, the operator could plan for its network to handle increasing amounts of video type traffic, which has specific technical requirements that are totally different to, say, email traffic.
Spying is complying
We also can’t forget another reason for mobile phone monitoring – the fact that companies are instructed to do it. Following the terrorist attacks of 9/11 and those in Madrid and London, the EU introduced the Data Retention Directive. This requires all telecommunications providers to monitor and retain certain metadata that records our technology use.
If we want to keep using technology such as mobile phones, and there is plenty of evidence to suggest we do, then we have to accept that such technology will track our movements. We then need to ask what should be done with the metadata that is being recorded.
We expect a mobile operator to provide a quality service and offer high levels of customer care, both of which are underpinned by the metadata they hold. Similarly, if we perceive that the country is at risk from terrorist and criminal threats then surely, we should allow the state access to metadata that allows it to detect and defeat those threats.
The counter argument is that such metadata, and access to it, goes against basic human rights of privacy. In reality, we cannot have it all ways and striking the right balance is a key dilemma for governments the world over as well as for mobile phone customers.