Australians expect paper-based elections to provide privacy, integrity and transparency. Why should we abandon these principles just because the election uses a magical device called a computer?
The iVote system used in last month’s NSW state election introduced large-scale Internet voting to Australia. The overwhelming majority of its 47000 votes were cast from interstate and overseas.
iVote was initially intended only for visually impaired voters, so the eventual number of votes exceeded expectations by a factor of ten.
Although there have been several Internet voting pilots worldwide, only Estonia and Switzerland use Internet voting regularly and on a large scale for public elections.
Internet voting remains controversial, with security the overriding concern. Security holes could compromise vote privacy or cause a vote to be cast that did not reflect the voters’ intention, was not properly transmitted, or was not correctly counted.
In the Netherlands, once one of the foremost practitioners of e-voting, the concerns were so great that Internet voting and voting machines were recently abandoned.
Security guru Bruce Schneier states, “Building a secure Internet-based voting system is a very hard problem, harder than all the other computer security problems we’ve attempted and failed at. I believe that the risks to democracy are too great to attempt it.”
Was iVote secure enough to be trusted with 47000 votes? Can it be trusted for its 900 votes in the seat of Balmain, in which changing about 100 votes would have changed the outcome? We honestly don’t know, because minimal information about iVote has been publicly released so far.
In particular no technical details are available on how it works and how security was evaluated, and it may well be the case that these will never be publicly known. We do know that taking votes in an unverifiable clandestine process would be unacceptable whatever technology was being used.
The problem of distrusting a voting system’s integrity is not new, and is not unique to computers. In Australian paper-based elections we mitigate this problem by using well-understood and highly transparent security procedures that are verified by multiple opposing scrutineers.
This rigorous scrutiny is highly likely to detect and prevent fraud and human error. It improves election integrity, and it convinces the public that the entire process is robust and trustworthy.
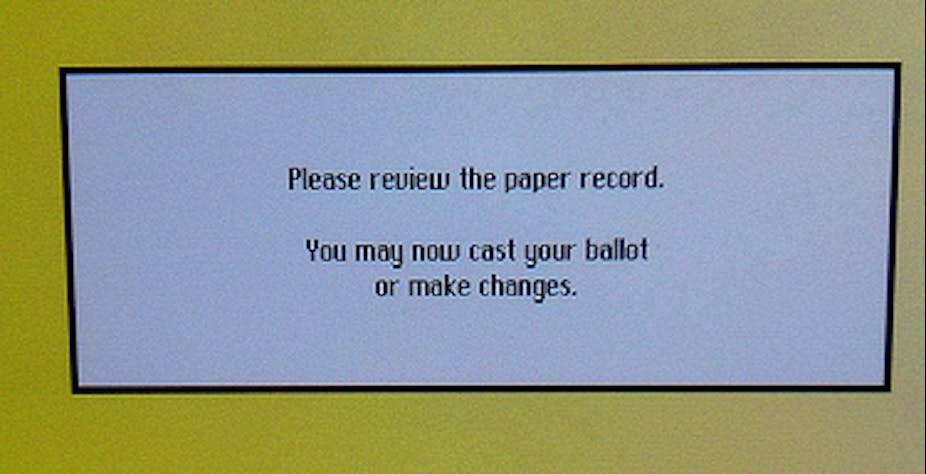
Verifiability is much more difficult in Internet voting because a person cannot directly observe what the computer is doing. Even if the software is carefully scrutinised, this doesn’t guarantee that it is error-free or that it is indeed the code actually running.
Furthermore there are fewer physical limitations to prevent fraud or error occurring on a large scale. A single person who gains access (authorised or not) to the Internet voting servers can potentially learn how each person voted or even change the votes.
What can be done about this? Researchers are actively developing advanced cryptographic protocols for Internet voting that provide strong secrecy and verifiability, thereby preventing many attacks. But some serious attacks still cannot be countered by cryptographic techniques alone.
In addition to cryptographic techniques, it is essential to apply the time-honoured principles of high transparency and intense scrutiny to Internet voting systems, including their source code, all documentation and reports, and the associated physical security procedures. This should be available to e-voting and security experts and the public. Scrutiny improves security because it allows problems to be identified and rectified.
It would allow us to make rational decisions about the appropriate balance between security and convenience. Transparency has been highly effective so far in developing trustworthy democratic elections, and should remain fundamental to the continual evolution of elections in the future.