The current health crisis has led to a rise in the use of digital services. Telework, along with school closures and the implementation of distance learning solutions (CNED, MOOCs, online learning platforms such as Moodle for example), will put additional strain on these infrastructures since all of these activities are carried out within the network. This raises concerns about overloads during the lockdown period. Across the Internet, however, DNS server loads have not shown a massive increase in traffic, therefore demonstrating that Internet use remains under control.
The Internet is a network that is designed to handle the load. However, telework and distance learning will create an unprecedented load. Simple measures must therefore be taken to limit network load and make better use of the Internet. Of course, these rules can be adapted depending on the tools you have at your disposal.
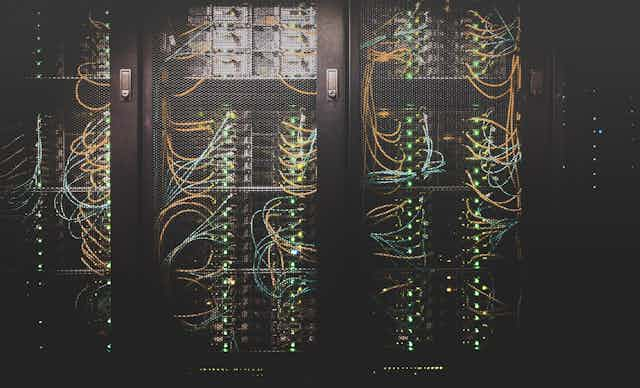
How do telecommunications networks work?
The Internet network functions by sending packets between machines that are connected to it. An often-used analogy is that of the information highway. In this analogy, the information exchanged between machines of all kinds (computers, telephones and personal assistants, to name just a few) is divided into packets (small and large vehicles). Each packet travels through the network between a source and a destination. All current networks operate according to this principle: Internet, wireless (wi-fi) and mobile (3G, 4G) networks etc.
The network must provide two important properties: reliability and communication speed.
Reliability ensures accurate communication between the source and the destination, meaning that information from the source is transmitted accurately to the destination. Should there be transmission errors, they are detected and the data is retransmitted. If there are too many errors, communication is interrupted. An example of this type of communication is e-mail. The recipient must receive exactly what the sender has sent. Long packets are preferred for this type of communication in order to minimize communication errors and maximise the quantity of data transmitted.
Communication speed makes real-time communication possible. As such, the packets must all travel across the network as quickly as possible, and their crossing time must be roughly constant. This is true for voice networks (3G, 4G) and television. Should a packet be lost, its absence may be imperceptible. This applies to videos or sound, for example, since our brain compensates for the loss. In this case, it is better to lose a packet from time to time – this leads to communication of lower quality, but they remain usable in most cases.
Congestion problems
The network has a large overall capacity but it is limited for each of its components. When there is very high demand, certain components can become congested (routers, links and servers). In such cases, the two properties (reliability and speed) can break down.
For communications that require reliability (web, e-mail), the network uses the TCP protocol (TCP from the expression “TCP/IP”). This protocol introduces a session mechanism, which is implemented to ensure reliability. When a packet is detected as lost by its source, it is retransmitted until the destination indicates that it has arrived. This retransmission of packets exacerbates network congestion, and what was a temporary slowdown turns into a bottleneck. To put it simply, the more congested the network, the more the sessions resend packets. Such congestion is a well-known phenomenon during the “Internet rush hour” after work.
If the source considers that a communication has been subject too many errors, it will close the “session.” When this occurs, a great quantity of data may be lost, since the source and the destination no longer know much about the other’s current state. The congestion therefore causes a wastage of capacity, even once it is over.
For communications that require speed (video, voice), the network instead uses the UDP protocol. Unfortunately, routers are often configured to reject this kind of traffic in the event of a temporary overload. This makes it possible to prioritize traffic using sessions (TCP, email, web). Losing a few packets in a video or voice communication is not a problem, but losing a significant amount can greatly affect the quality of the communication. Since the source and destination exchange only limited information about problems encountered, they may have the impression that they are communicating when this is not actually the case.
The following proposals aim to limit network load and congestion, in order to avoid a situation in which packets start to get lost. It should be noted that the user may be explicitly informed about this loss of packets, but this is not always the case. It may be observed following delays or a deterioration of communication quality.
What sort of communications should be prioritized in the professional sphere?
Professional use must prioritise connection time for exchanging e-mails or synchronising files. But the majority of work should be carried out without being connected to the network, since for a great number of activities, there is no need to be connected.
The most crucial and probably most frequently used tool is e-mail. The main consequence of the network load may be the time it takes to send and transmit messages. The following best practices will allow you to send shorter, less bulky messages, and therefore make e-mail use more fluid:
Choose thick clients (Outlook, Thunderbird for example) rather than web-based clients (Outlook Web Access, Zimbra, Gmail for example) since using e-mail in a browser increases data exchange. Moreover, using a thick client means that you do not always have to be connected to the network to send and receive e-mails.
When responding to e-mail, delete nonessential content, including attachments and signatures.
Delete or simplify signatures, especially those that include icons and social media images.
Send shorter messages than usual, giving preference to plain text.
Do not add attachments or images that are not essential, and opt for exchanging attachments by shared disks or other services.
When it comes to file sharing, VPNs (for virtual private networks) and cloud computing are the two main solutions. Corporate VPNs will likely be the preferred way to connect to company systems. As noted above, they should only be activated when needed, or potentially on a regular basis, but long sessions should be avoided as they may lead to network congestion.
Most shared disks can also be synchronized locally in order to work remotely. Synchronization is periodic and makes it possible to work offline, for example on office documents.
Keeping in touch with friends and family without overloading the network
Social media will undoubtedly be under great strain. Guidelines similar to those for e-mail should be followed and photos, videos, animated GIFs and other fun but bulky content should only be sent on a limited basis.
Certain messages may be rejected by the network. Except in exceptional circumstances, you should wait for the load to ease before trying again.
Advertising represents a significant portion of web content and congests the network without benefits for the user. Most browsers can incorporate extensions (privacy badger) to delete such content automatically. Some browsers, such as Brave for example, also offer this feature. In general, the use of these tools does not have an impact on important websites such as government websites.
Television and on-demand video services also place great strain on the network. When it comes to video, it is preferable to use TNT (terrestrial network) instead of boxes, which use the Internet. The use of VoD services should be limited, especially during the day, so as to give priority to educational and work applications. And a number of video services have limited their broadcast quality, which significantly reduces bandwidth consumption.
Cybercrime and security
The current crisis will unfortunately be used as an attack tool. Messages about coronavirus must be handled with caution. Such messages must be read carefully and care must be taken with regard to links they may contain if they do not lead to government websites. Attachments should not be opened. The Hoaxbuster website and the Décodeurs application by the Le Monde newspaper can be used to verify whether information is reliable.
At this time in which online meeting systems are extensively used, attention must be given to personal data protection.
The website of ARCEP (France’s regulator for telecom operators) provides guidelines for making the best use of the network. To best protect yourself from attacks, the rules for IT security established by the French cybersecurity agency ANSSI are more important than ever.