
Articles on Cryptography
Displaying 1 - 20 of 45 articles

A major focus of the federal government’s defence policy update is the need to develop quantum-based defence technology that will help Canada address two big threats: the Arctic and cyber security.

A flawed paper shakes confidence in the foundations of ‘quantum-proof’ encryption – and highlights the need for a new generation of experts.

End-to-end encryption provides strong protection for keeping your communications private, but not every messaging app uses it, and even some of the ones that do don’t have it turned on by default.
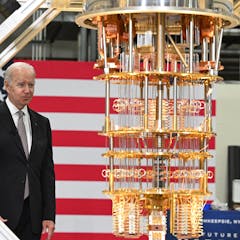
Several companies have made quantum computers, but these early models have yet to demonstrate quantum advantage: the ability to outstrip ordinary supercomputers.

Habsburg emperor Rudolf II owned a spirit-summoning alchemical hand bell. We want to decipher its cryptic Greek inscriptions.

To protect against future quantum cyber attacks, two technological paths are being explored. Decryption.
Canada is well positioned to gain far-reaching economic and social benefits from the rapidly developing quantum industry, but it must act now to secure its success.

A mathematician explains how language can keep your online accounts safe and pinpoint your location on the planet.

Australians vote on a piece of paper and put that into a box which is then counted. We don’t know how to replicate this transparent, verifiable process over the internet.

The secret recipe came from Arthur Dee, 17th-century alchemist and royal physician to the Tsar.

Researchers tried several times to have the document declassified, including in 1992, 2004 and 2016. It was initially written to help American NSA agents crack difficult coded messages.

NFTs are made the same way as crypto coins, but where every crypto coin is like every other, each NFT is a unique digital item – from images to sound files to text.

A paper published by researchers at Google claimed that they had achieved computing quantum supremacy, but leaks and counter-claims have created a stir.

On October 23 Google announced that it built a quantum computer thousands of times faster than classic computers. This could have immense impacts on finance, cryptography and other fields.

Computer capabilities have boosted our decryption technology to great heights. How will the future compare to a past, one in which codes were thought to be a means of communicating after death?

The Voynich Manuscript has researchers, the media, and the public hooked. But pseudo-explanations for the book’s ‘code’ reveals a serious problem with society’s relationship with science.

It is hard to predict when quantum computers will be strong and fast enough to crack the codes that keep bitcoin safe. But that day is coming.

Prime numbers are a mathematical mystery.

Crypto cash is catnip for criminals and a huge challenge to law enforcement – so it’s time to bring in a tough, jurisdiction-busting regulatory body.

Scholars dig in to the debate on whether police should be able to defeat or circumvent encryption systems.
